




There’s no worries about file sizes or data breaches using our military-grade 256-bit Advanced Encryption Standard (AES) security.
SendThisFile allows you to request files safely from someone with a simple email request.
“In our practice, we are always cognizant of information security, which is why we rely on SendThisFile as a secure means of file transfer in our organization.”
“SendThisFile technology enables us to handle over 2.3 terabytes of data and more than 14,000 file transactions per month without the need for additional corporate staff.”
“In our practice, we are always cognizant of information security, which is why we rely on SendThisFile as a secure means of file transfer in our organization.”

“SendThisFile technology enables us to handle over 2.3 terabytes of data and more than 14,000 file transactions per month without the need for additional corporate staff.”
Start by creating your free account and sign in.
Choose the file you want to upload and who receives it.
Relax as we automatically inform your recipients with easy instructions to access the file.
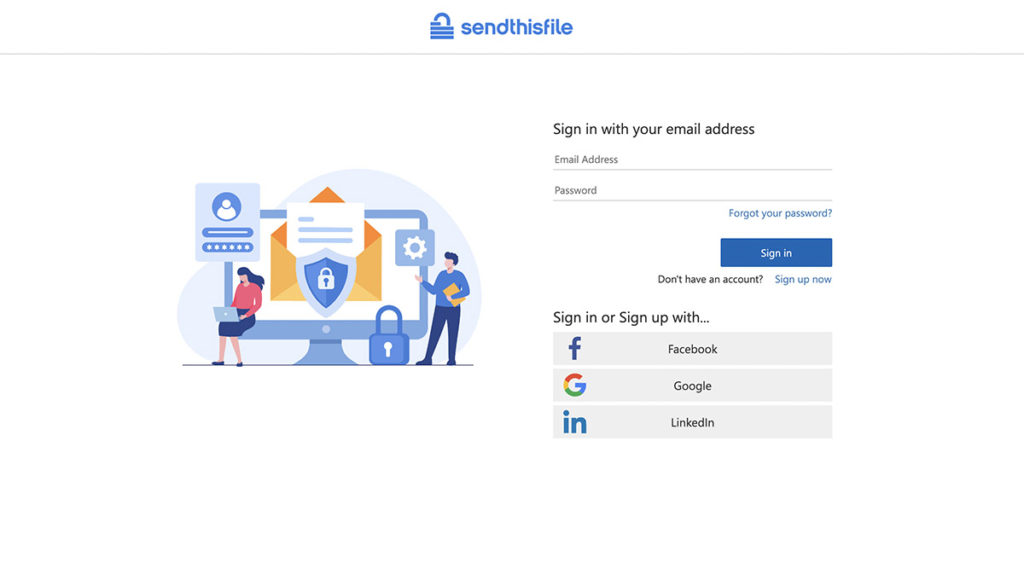
With no credit card required, create your new free account to start sending securely today. Upgrade to a Standard or Business plan at anytime.
Phone: (855) 736-3844 | +1 (316) 942-4707 | Contact Us